What is a PCAP file?
Analyzing packet captures – typically referred to as PCAPs - is critical for teams responsible for hunting threats, solving network outages, or tracking down performance issues.
PCAP files contain critical, packet-level evidence and vital clues into the root cause of a wide range of issues occurring on the network. Being able to save and share that evidence in a portable PCAP file format can be essential for IT, network and security operations teams. This primer explains all you need to know about PCAP files.
- Contents
- What is a PCAP File?
- What Can Read or Save a PCAP?
- Understanding the PCAP File Format
- PCAP File Packet Records
- Limitations of the PCAP File Format
- Is There an Alternative to PCAP Files?
- Are PCAPs a Security or Privacy Risk?
- How Do You Search and Manage PCAP files?
- Automating PCAP retrieval
- Conclusion
What is a PCAP File?
PCAP files are a common format for storing packet captures. A PCAP file includes an exact copy of every byte of every packet as seen on the network, including OSI layers 2-7.
The PCAP file format was developed alongside the development of the tcpdump and libpcap libraries in the 1990s. PCAP files are easily read by a variety of different tools and software programs, they are an easy way to share or save packets you have captured from any copper, fibre, or wireless network.
For a complete guide to Packet Capture see our introduction here.
What Can Read or Save a PCAP?
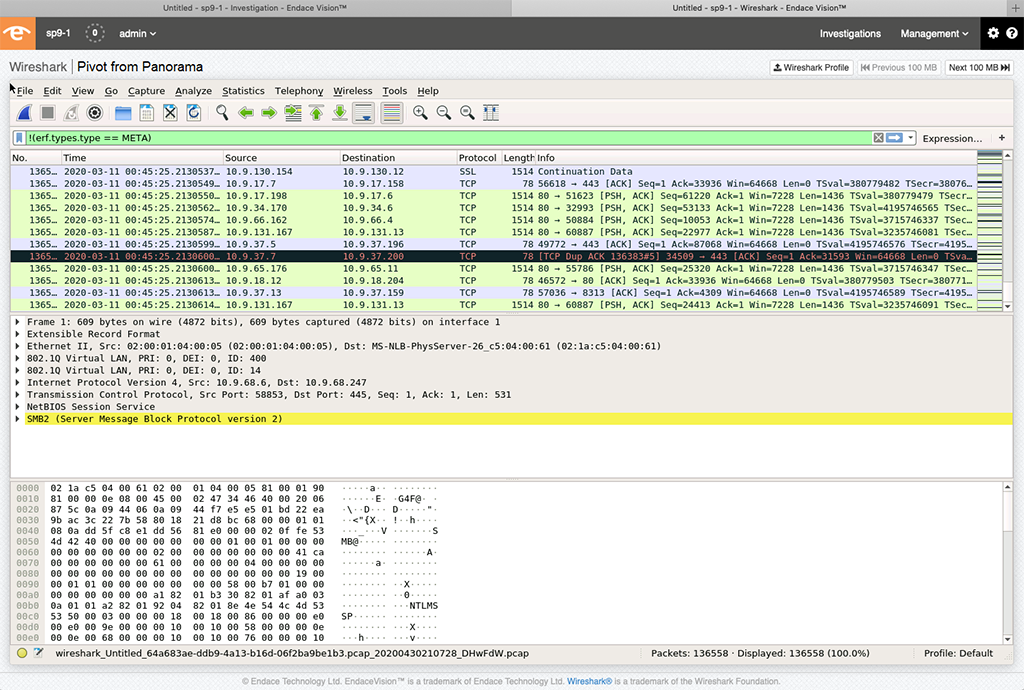
Packet capture systems (such as our EndaceProbe) can read and/or write PCAP format files, as can open-source tools including tcpdump, libPCAP, WinPCAP, NPCAP, Zeek, Snort, Suricata, Wireshark and a variety of other commercial packet sniffers and protocol analysers. Many tools such as firewalls, virus scanners, threat detection tools, as well as threat analysis websites like VirusTotal can read or write PCAP files too.
Understanding the PCAP File Format
The PCAP file structure includes a file header followed by zero or more packet records.
PCAP file headers

What do these terms mean?
Magic Number
- If Magic Number = 0xA1B2C3D4 Timestamp is seconds and microseconds.
- If Magic Number = 0xA1B23C4D, Timestamp is seconds and nanoseconds.
SnapLen
The SnapLen (snap length) is the maximum number of octets captured from each packet.
LinkType
LinkType contains a value - assigned by tcpdump.org – that describes the type of link the packets were captured from. For example, a value of 1 = IEEE 802.3 Ethernet. For more information about LinkTypes see Tcpdump.org
FCS and F
FCS stands for Frame Check Sequence. If the "F" bit is set (true), then the three bits in the FCS field provide the number of 16-bit (2 byte) words of FCS that are appended to each packet. Ethernet typically has a value of 2 indicating 32 bit FCS.
PCAP File Packet Records
In a PCAP file, the file header is followed by a series of packet records. Each packet record represents a single packet captured from the network, along with a timestamp, the length of the packet, and the length captured from that packet.

The Ethernet Frame Checksum (FCS) may or may not be captured. If the FCS is not present the captured packets can still be assumed to be valid, however packets with errors may have been dropped. If the FCS is present, the reader can check if there was an error for each packet.
Key Packet Record Fields
- Timestamp (Seconds): the number of seconds that have elapsed since 1970-01-01 00:00:00 UTC
- Timestamp (Microseconds or nanoseconds): the number of microseconds or nanoseconds that have elapsed since the last full second.
- Captured Packet Length: the number of octets captured from the packet, if packets are truncated this value is the length of the truncated packet.
- Original Packet Length (32 bits): the actual length of the packet when it was transmitted on the network.
Limitations of the PCAP File Format
The PCAP file is a simple flat file with no index and no extensibility. PCAP files were never designed for managing packet captures larger than a few hundred Mbytes. Beyond this point reading, filtering, and searching a PCAP file can become a slow and tedious exercise – as anyone who’s opened a large PCAP file in Wireshark will tell you!
There is no “Provenance” built into PCAP files to record how and where the packets were captured. That can make it easy to lose track of where and when the packets were captured and the state of the system they were captured from at the time. During a legal cross examination or a forensic investigation the source of a PCAP may be difficult to authenticate.
Is There an Alternative to PCAP Files?
Yes there is. Despite the fact that the PCAP format was invented in the 1990’s, it remains the most widely used open format for storing and sharing packet captures. However, there are other formats that provide additional functionality including a next generation format popularized by Wireshark.
- PCAPNG (PCAP Next Generation) is more extensible and portable than PCAP and has a more flexible file structure. It also includes additional information about the packet, and the interface used to capture the packet, such as drop counters, DNS records, etc.
- ERF, Extensible Record Format adds provenance metadata, high resolution timestamps and in-band packet loss auditing. Provenance metadata embedded in an ERF file enables forensics teams to know exactly where the ERF file originated from since it includes critical information such as the originating system name and system status embedded within the file.
All three formats are happily accepted by WiresharkTM and also by many other protocol analysis tools.
Are PCAPs a Security or Privacy Risk?
PCAPs are ideal for sharing a small number of packets related to a specific investigation due to their simplicity and ubiquitous nature. But their very ease of use and portability brings with it the potential for information leakage and associated cybersecurity and privacy risks.
- PCAPs are clear-text copies of potentially unencrypted private and/or sensitive information transferred over a network. Someone that has access to the PCAP may be able to reassemble the data or files contained within the packets, or even extract sensitive information such as passwords, usernames, or other information that could be damaging if made public.
- Malware or other types of malicious content may be contained within the packets residing in a PCAP file, so care must be taken when handling such files so as not to infect other computer systems.
- Emailing or saving a PCAP may trigger virus scanners or IDS/IPS systems.
- Replaying or reassembling a PCAP could unleash damaging malware - so such actions should only be done carefully in a protected or sandboxed environment by properly trained staff.
The data in PCAPs may be classified as protected information under the laws of various state or federal governments including GDPR, ADPPA, HIPAA, etc, and saving a PCAP may be deemed as collecting private information.
When saving or storing PCAP files organisations should take the same care as they would with any other sensitive information.
Security can be enhanced when PCAPs are strongly encrypted with password security and stored in a secure location with restricted access. Access to systems that can generate PCAPs should be tightly controlled with privileges assigned only to staff with appropriate clearance.
How Do You Search and Manage PCAP files?
Keeping track of what resides in particular PCAP files can be challenging when the data is managed in potentially hundreds of individual files – particularly when using the PCAP file format which lacks Provenance data. Careful naming of PCAP files becomes very important.
A better approach is to store packet data on a dedicated packet capture appliance with indexing which enables fast searching across large volumes of packet data and allows smaller PCAP files to be extracted or exported on-demand for detailed analysis or archival as required.
Automating PCAP retrieval
Large security teams with distributed packet capture environments can also benefit from automated PCAP retrieval. This enables a platform - such as a SOAR tool - to automate the retrieval of PCAPs when an alert is received from other tools such as IDS or IPS systems.
This is a great way to ensure important PCAP files can be retrieved and stored permanently in a secure location so it is there when an analyst is available to investigate the issue. However, as noted above, care must be taken to ensure access to any exported PCAP files is secured to avoid the risks identified above.
Conclusion
PCAP files are a simple and ubiquitous way to capture and share information about any threat or network event. Teams that leverage packet capture benefit from faster and more precise incident response, and quicker resolution of cyber incidents, performance issues and network outages.
However it’s important to take care when storing and handing PCAPs as they may contain sensitive information, malware or threats.

Who is Endace?
Endace specializes in scalable, high-speed, high-performance packet capture. Our solutions are used by some of world’s biggest organizations on some of the fastest networks on the planet.
If you are looking for a packet capture solution, we’d love to show you why Endace is the best choice. Contact us to book a demo or ask a question.